Cyber Threat Intelligence
Dark Web Search
Dark Web Mention Monitoring
Employee Email Breach Monitoring
Compromised Employee Device Monitoring
Compromised Client Credential Monitoring
Compromised Payment Credential Monitoring
Executive Threat Monitoring
Threat Actor Intelligence
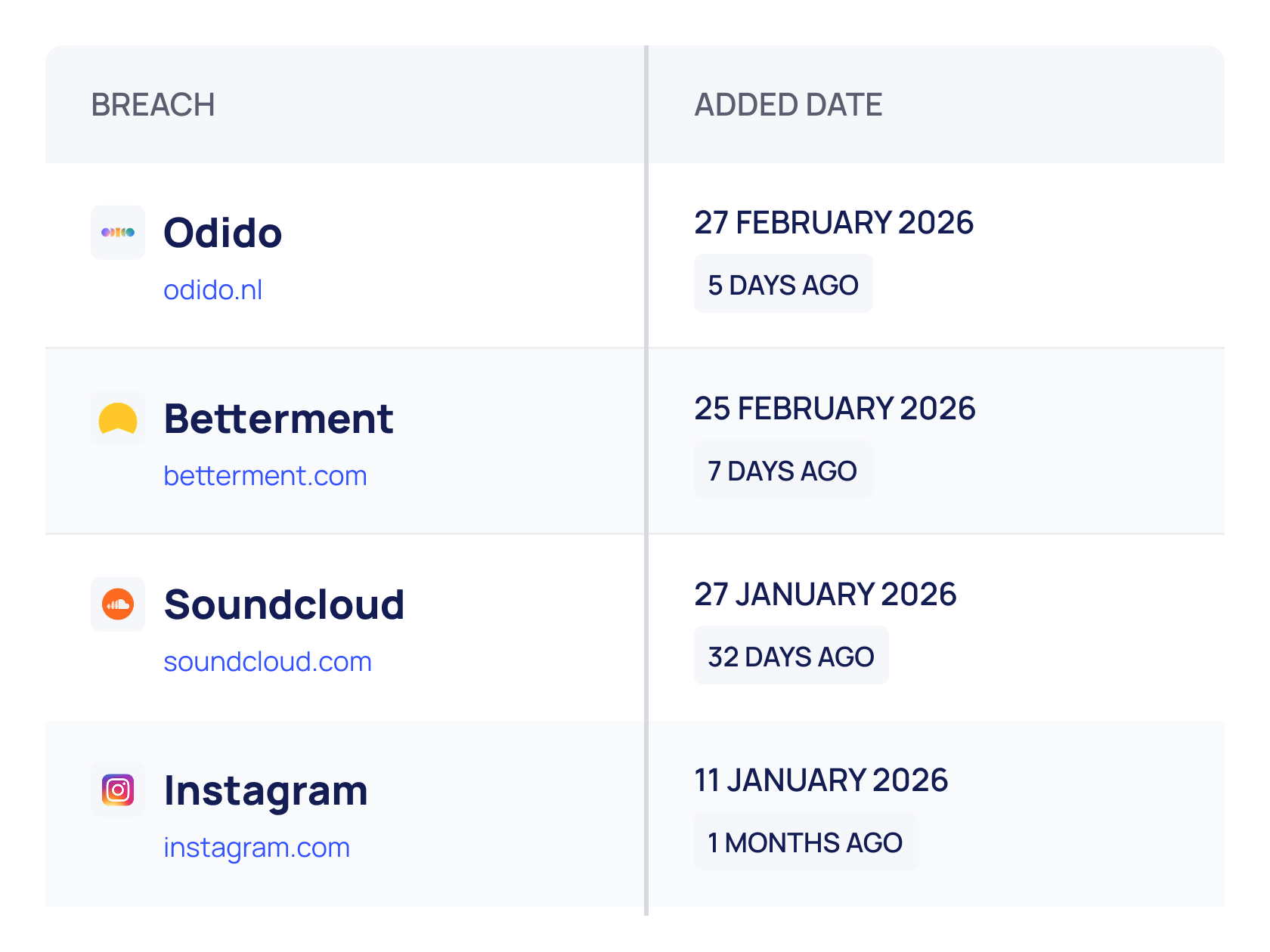
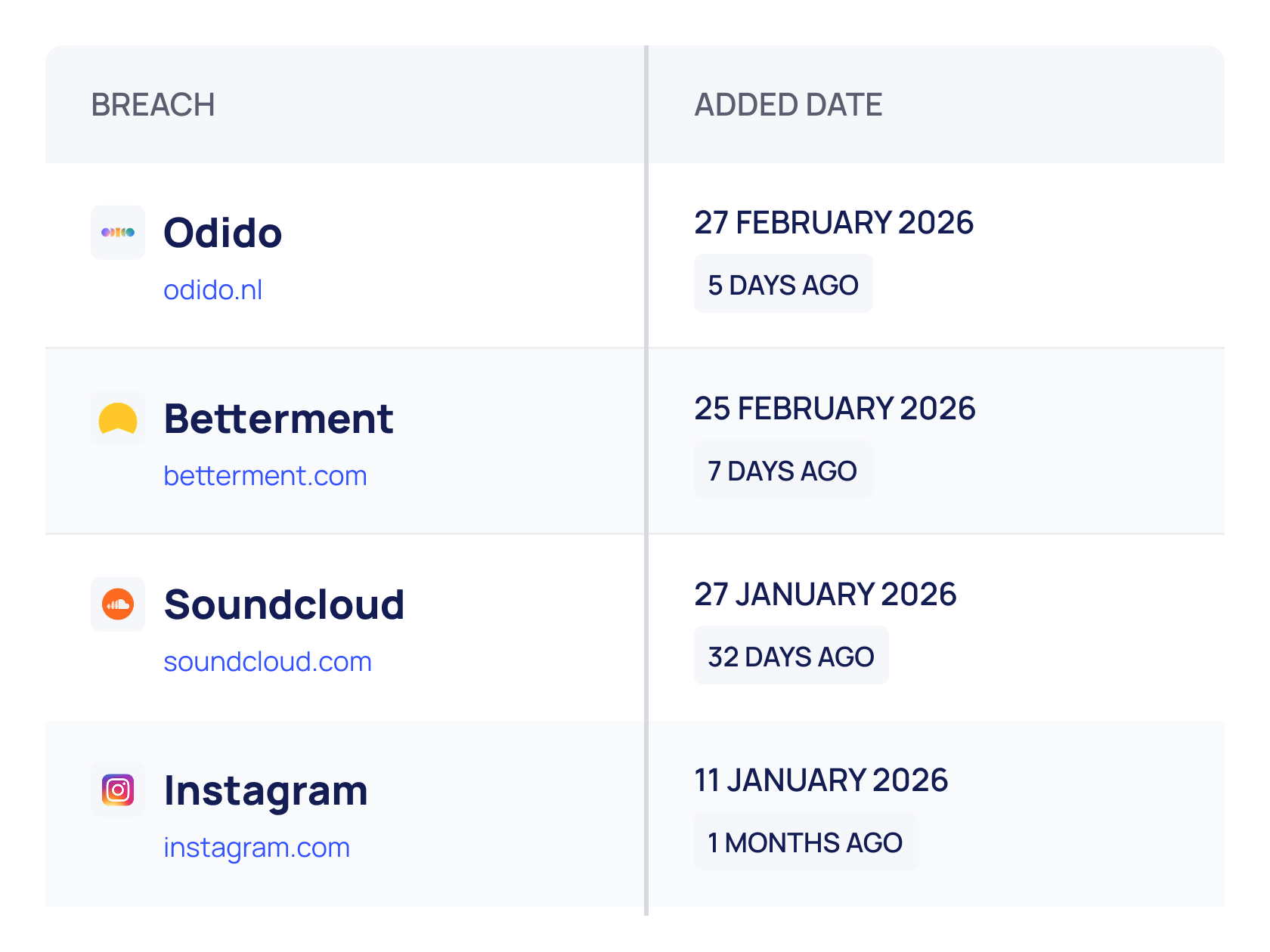
Data Breach Index
IOC Feeds
Cybersecurity News
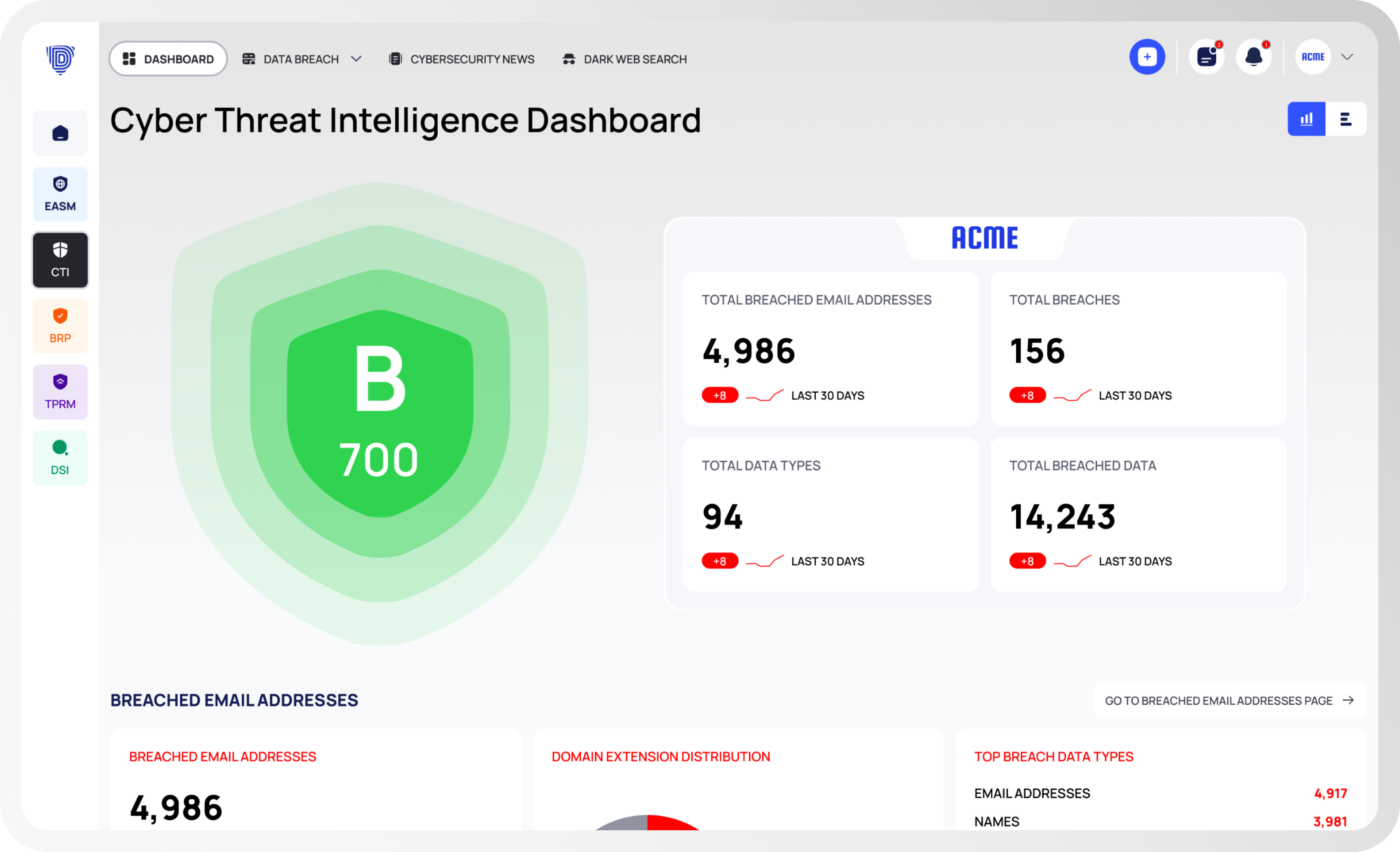
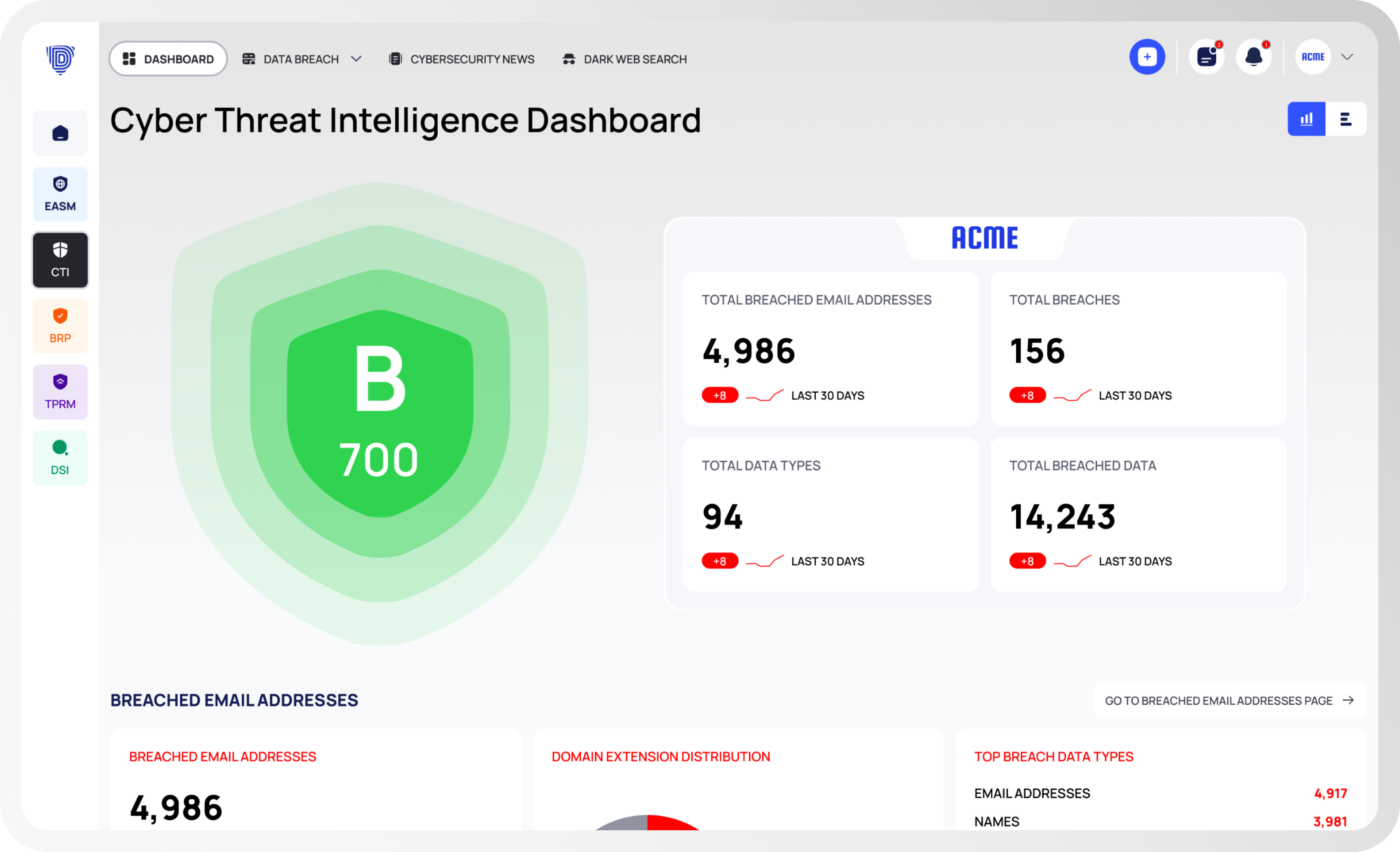
Cyber Threat Score
Reports
Produce detailed reports covering dark web findings, breach exposure, threat actor activity, and CTI scoring. Reports are structured for different audiences: technical detail for analysts, executive summaries for leadership, and compliance-ready documentation for auditors. All reports reflect current data from the Deepinfo Platform.
Notifications
Configure notification rules to trigger on new dark web mentions, newly detected breaches, executive-targeted threats, or changes in your CTI score. Set severity thresholds and scope notifications by category so your team receives actionable signals aligned with their operational priorities.
APIs
Access the same intelligence available in the platform through comprehensive APIs. Automate threat data ingestion into your SIEM, SOAR, ticketing, or internal systems. Pull specific intelligence on demand, trigger workflows based on new findings, or build custom integrations. The API delivers the same continuous intelligence as the platform interface.
Request Demo
Trusted by leading companies worldwide, the Deepinfo Security Platform is the preferred choice for continuously managing cyber threat exposure.